Trend Micro’s Zero Day Initiative’s annual Pwn2Own hacking competition began on Wednesday, with 2 Safari exploit attempts, one of which proved successful.
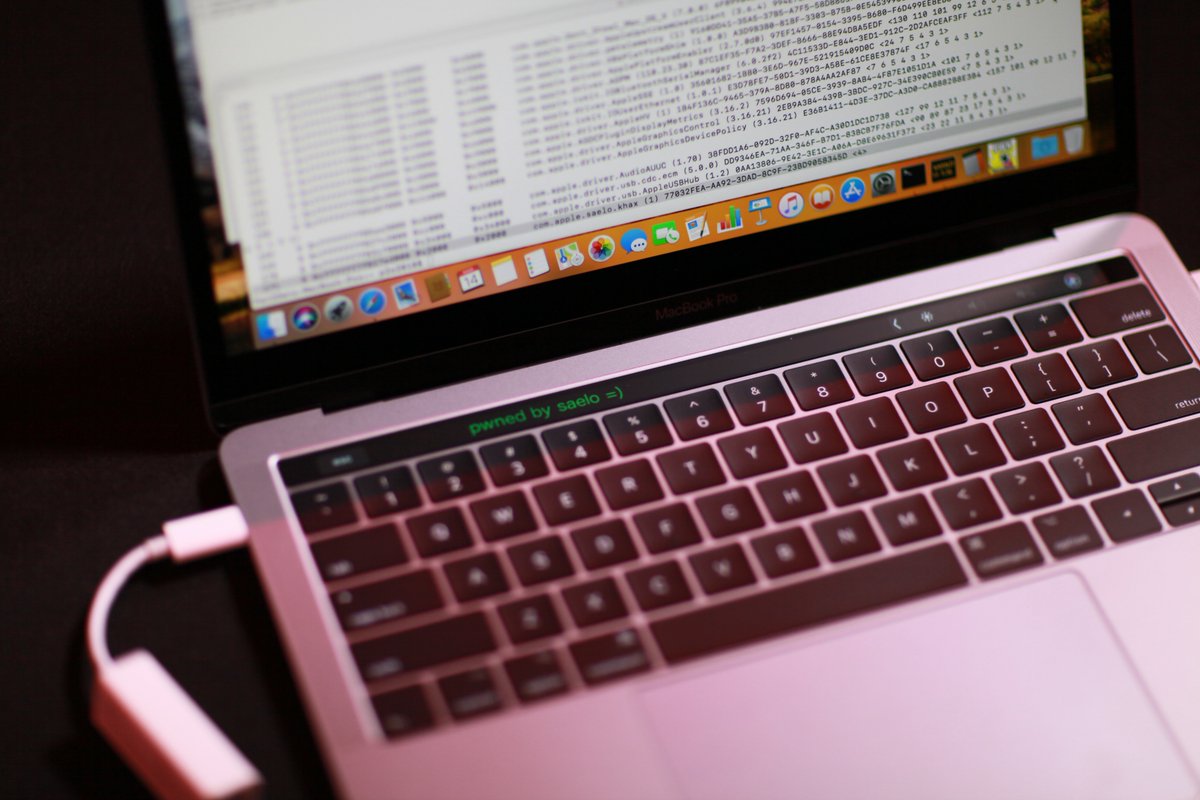
Samuel Groß (5aelo) of phoenhex targeting Apple Safari with a macOS kernel EoP
Success: Samuel used a three bug chain to successfully exploit Apple Safari, earning himself $65,000 and 6 points toward Master of Pwn.
Samuel’s exploit modified the text on a MacBook Pro’s touchbar, as seen in the above image.
A separate hacking attempt was attempted against Safari by Richard Zhu, who was unable to get his sandbox escape attempt running within the 30 minute time limit allotted by the competition rules. Zhu had successfully bypassed iPhone 7 security protocols using two Safari bugs at the Mobile Pwn2Own event in November.
Zhu was successful on Wednesday with an exploit targeting Microsoft Edge, via a Windows kernel EoP. Zhu used two UAFs in the browser and an integer overflow in the kernel to earn $70,000 USD and 7 points towards Master of Pwn.
Pwn2Own is an annual hacking contest, which began in 2007, and encourages security researchers to discover, share, and demonstrate zero-day security flaws on software and hardware. Successful contestants get to keep the device they attacked and also receive a cash prize. Points are also awarded, which if enough of them are accumulated, go toward a “masters” jacket.
Hardware and software vendors benefit from the competition by gaining information about vulnerabilities in their software and hardware, and gain the chance to patch this holes before they are widely exploited.
Day two of Pwn2Own takes place on Thursday, and will feature two more attempts against Safari. Markus Gaasedelen, Nick Burnett, Patrick Biernat of Ret2 Systems, Inc. will target Apple Safari with a macOS kernel EoP, while MWR Labs – Alex Plaskett (AlaxJPlaskett), Georgi Geshev (munmap), Fabi Beterke (pwnfl4k3s) will target Apple Safari with a sandbox escape.