There is a new Mac ransomware variant hitting Macs through pirated apps. A new report from Malwarebytes says a new “EvilQuest” Mac ransomware variant was found in a pirated version of the Little Snitch app found on a Russian forum.
The illicit version of Little Snitch uses a generic installer package, which installs the real version of the app but also installs an executable file named “Patch” into the /Users/Shared directory and a post-install script for infecting a machine.
The Patch file is moved by the installation script into a new location, renaming it to “CrashReporter,” which is a legitimate macOS process. That keeps it hidden in Activity Monitor. the patch file then installs itself in numerous locations on the Mac.
The ransomware encrypts settings and data files on the Mac, like Keychain files, resulting in an error when attempting to access the iCloud Keychain. During testing by Malwarebytes, the Finder also malfunctioned and problems were experienced with the Dock and other apps.
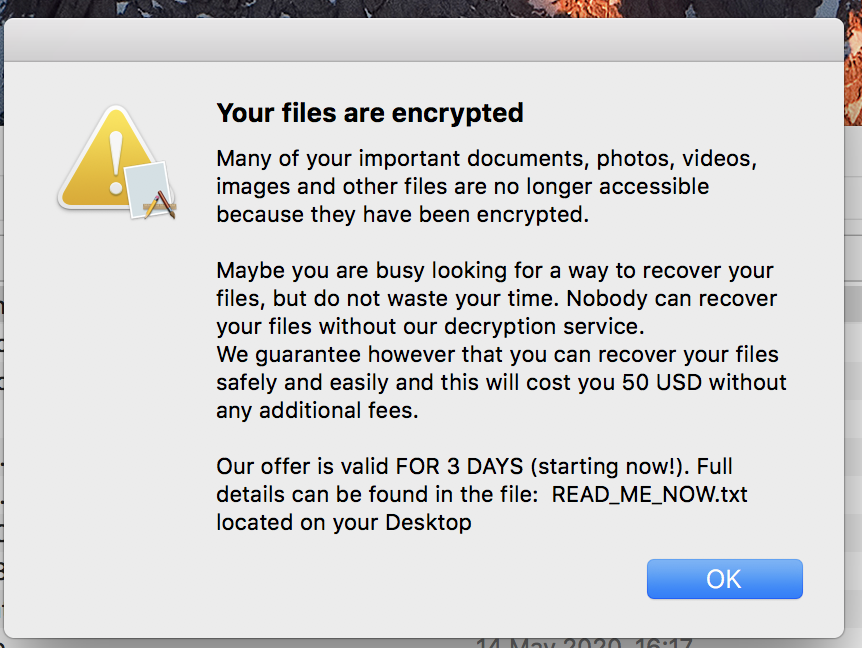
Malwarebytes says the ransomware worked poorly and no instructions on paying the ransom were found, although a screenshot found on the forums where the malicious software originated suggests it’s meant to prompt users to pay $50 to recover access to their files. Please note: do not pay the ransom if your Mac is infected, as it does not result in the removal of the malware.
The malware may also install a keylogger to monitor your keystrokes, but what it does with that information is unknown. While Malwarebytes says that its software for the Mac will remove the ransomware, which is detected as Ransom.OSX.EvilQuest. However, encrypted files will require a restore from a backup. You have a backup, right? But you don’t download pirated apps anyway, right?
(Via MacRumors)

