A now patched iOS WiFi vulnerability could have allowed hackers to remotely access nearby iPhones and gain control of the device.
Ian Beer, a researcher at Project Zero, Google’s vulnerability research team, discovered the exploit, which used a vulnerability in Apple Wireless Direct Link (AWDL), Apple’s proprietary mesh networking protocol that enables things like AirDrop and Sidecar to work.
Beer disclosed the exploit. to the public on Tuesday, via a 30,000-word blog post, which details how an AWDL memory corruption bug could give attackers remote access to a user’s device. Access would give the attacker access to a user’s personal data, including photos, emails, messages, and even passwords and crypto keys stored in the keychain.
Beer discovered the vulnerability in a 2018 iOS beta that Apple accidentally shipped without stripping function name symbols from the kernelcache. This offered a load of missing context about how bits of code fit together.
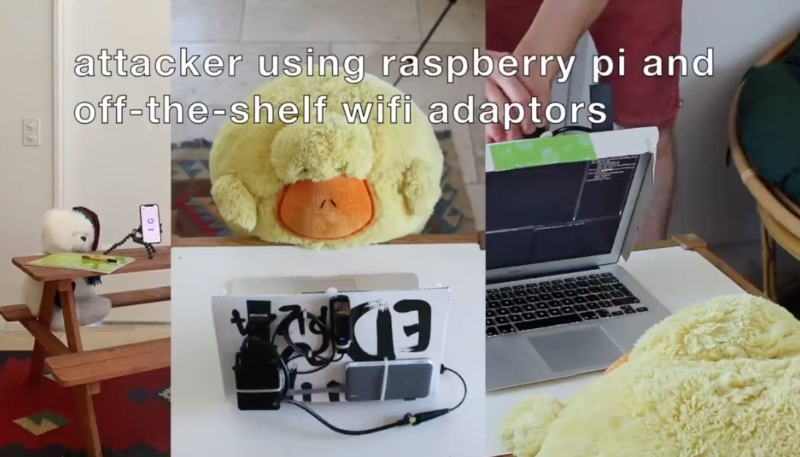
After investigating the code, Beer was able to find code related to AWDL, identify the vulnerability, and then attempt to exploit it remotely, with the use of a laptop, WiFi adapters, and a Raspberry 4B.
While it took Beer six months to develop an exploit for the flaw, when he was finished, he was able to hack any iPhone that was in radio length, run code on it, and steal user data from the device.
Project Zero founder Chris Evans told ArsTechnica that it’s scary to think that the exploit works without any user interaction at all, and users never have a clue that their privacy was violated.
This attack is just you’re walking along, the phone is in your pocket, and over Wi-Fi someone just worms in with some dodgy Wi-Fi packets.
Beer says he has no evidence that the issues he uncovered were exploited in the wild, but “we do know that exploit vendors seem to take notice of these fixes.”
The takeaway from this project should not be: no one will spend six months of their life just to hack my phone, I’m fine.
Instead, it should be: one person, working alone in their bedroom, was able to build a capability which would allow them to seriously compromise iPhone users they’d come into close contact with.
Imagine the sense of power an attacker with such a capability must feel. As we all pour more and more of our souls into these devices, an attacker can gain a treasure trove of information on an unsuspecting target.
The exploit is no longer available, as Apple patched the vulnerability in May with the release of iOS 12.4.7. (Apple cites Beer in the changelogs for several security updates.)
Wi-Fi
Available for: iPhone 5s, iPhone 6, iPhone 6 Plus, iPad Air, iPad mini 2, iPad mini 3, and iPod touch 6th generation
Impact: A remote attacker may be able to cause unexpected system termination or corrupt kernel memory
Description: A memory corruption issue was addressed with improved input validation.
CVE-2020-3843: Ian Beer of Google Project Zero
Beer was the researcher who in August 2019 detailed ‘one of the largest attacks against iPhone users ever’ in the form of hacked websites distributing iOS malware to users of the then-current iOS 12 operating system.